How Direct Private Peering Can Enhance your Network Security
- Cloud networking
- May 1, 2019
- RSS Feed
From routing policy mistakes to BGP hijacks, how do enterprise businesses secure their network to avoid emerging security threats?
83% of enterprise workloads will be in the cloud by 2020 and as more and more data is delivered between on-premises and public environments, the network perimeter is starting to change. With this comes new security challenges faced by enterprise businesses.
Network security issues often come about when Border Gateway Protocol (BGP) routes are compromised. Let’s break this down:
The internet is composed of a mesh of ISPs, each one represented by an Autonomous System (AS) that peer to each other using BGP. Routes are then exchanged through BGP between the various ASs. Each BGP-learned route is accompanied by an AS path. Think of this AS path as the trail you follow to reach the destination.
This example shows what an AS path would look like from a given enterprise business labeled “MyAS” traversing the internet to reach Amazon Web Services (AWS), AS 14618.
I
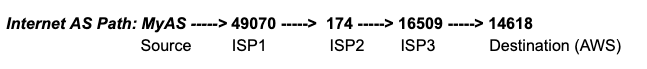
As you can see, there are three intermediary hops between the enterprise ‘MyAS’ and AWS ‘14618’. Each one of those ASs are also connected to multiple other ASs upstream which provides a highly interconnected network that is highly redundant and fault tolerant. Unfortunately, this also provides multiple opportunities for the company’s data to be rerouted and intercepted between the source and destination.
Oracle’s Internet Intelligence team monitors the internet for these interceptions and analyses the outcome. It could be a routing policy mistake that causes your traffic between Washington DC and Los Angeles to be routed through China. Or, a routing error could actually appear to be more intentional when Google, Facebook, Microsoft, and Apple traffic is routing through Russia.
Then, of course, there are blatant acts of cyber crime that happen more often than you might think. Take the April 2018 BGP hijack of Amazon’s DNS to steal cryptocurrency followed by the BGP hijack targeting payment systems in August. When attacks such as these happen, business impacts can result in anything from a disruption in services to data loss that could cost millions of dollars.
Traversing the open internet leaves data open to misdirection through BGP mishap. When migrating workloads from their private network to the public cloud, businesses need to make sure they are taking appropriate precautions to protect their data in transit.
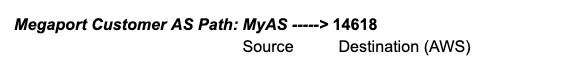
Establishing direct, private peering between networks can help mitigate this threat. Megaport provides this level of high-performance, dedicated connectivity that can be extended to both private and public services with the most popular cloud providers. Users can enjoy the security of peering between their source and destination without any intermediary ASs (as shown in this example):
As massive volumes of data continue to be pushed to the public cloud, new security threats will likely develop. Direct peering with Megaport can provide extra protection for those critical workloads without exposing data traversing your backend servers over the internet.
How does it work? Well, Megaport has direct API integrations with the world’s leading cloud providers. When connecting to your chosen cloud via Megaport, you’re peering with their direct connectivity product (for example, AWS Direct Connect) via a Virtual Cross Connect (VXC). The VXC forms the Layer 2 component of the connection. Layer 3 BGP connectivity is established directly between your network and the cloud.
For more information about the pitfalls of public internet connectivity, including security, read our blog post here. If you’d like to get in contact with us or have any further questions answered, go to our contact page.